College of Engineering
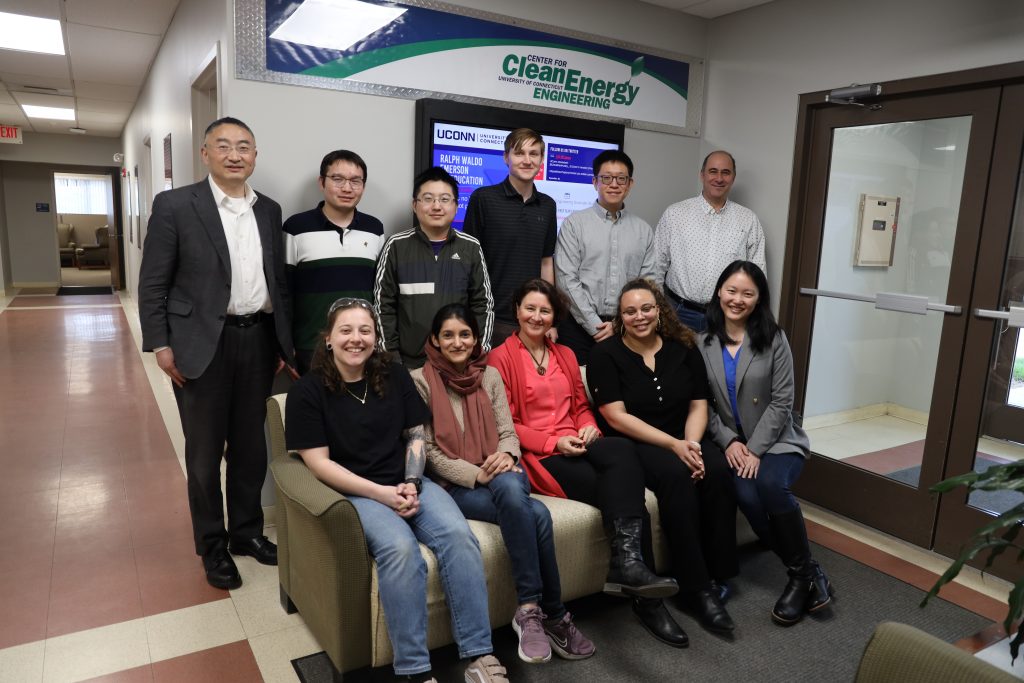
DOE Grants Fund Collaborative Clean Energy Projects
UConn is one of dozens of beneficiaries in funding program to bolster research into hydrogen energy and related projects
April 25, 2024 | Matt Engelhardt
UConn Provost Announces Awards for Excellence in Community Engaged Scholarship
The Provost’s Awards for Excellence in Community Engaged Scholarship (PAECES) recognize scholarly activities that integrate community engagement with research, creative work, and teaching
April 24, 2024 | Briana Huett, Associate Director of Outreach and Engagement
Pratt & Whitney Engineering Building Unveiled
Pratt & Whitney has strong ties to the UConn College of Engineering and UConn School of Mechanical, Aerospace and Manufacturing Engineering
April 22, 2024 | Claire Tremont
College of Engineering Names New Dean
Ji-Cheng ‘JC’ Zhao brings 30 years' experience working in academia, industry, and government
April 19, 2024 | Claire Tremont
Six UConn Faculty Members Named AAAS Fellows
The AAAS is the world’s largest general scientific society and publisher of the Science family of journals
April 18, 2024 | Mike Enright '88 (CLAS), University Communications
Meeting the High-Speed Challenge
The Air Force Research Laboratory awarded UConn an additional $10.5 million for projects related to welding and advanced materials for high-temperature applications
April 18, 2024 | Matt Engelhardt
UConn Celebrates Promotion and Tenure of 91 Faculty
Evaluations for promotion, tenure, and reappointment apply the highest standards of professional achievement in scholarship, teaching, and service for each faculty member evaluated
April 17, 2024 | Alexis Lohrey, Office of the Provost
Shining Light Makes Materials Magnetic at Room Temperature
In April, Engineering Professor Alexander Balatsky published his work applying AI to his theory of 'dynamic multiferroicity'
April 17, 2024 | Christie Wang, for the Office of the Vice President for Research
Engineering Entrepreneurship: Hacking For Defense
The course uses a project-based approach to get students out of the classroom and into the community, engaging with defense industry professionals
April 16, 2024 | Claire Tremont
UConn Leading Federally Backed Regional Initiative to Defend Electric Grid from Cyberattack
CyberCARED will take UConn’s cybersecurity research and development into a new domain
April 9, 2024 | Jaclyn Severance